Encryption is a mechanism by which you make things that are traditionally readable, unreadable. It’s the technology that helps keep those that should not be able to see something, from seeing something. As a security professional and privacy advocate, it’s a great thing!
As a parent, or a network administrator, charged with creating family-friendly internet it can be a challenging feature.
This article won’t touch on the merits of encryption, or whether it should, or should not be employed. Rather, it will focus on the technology and highlight how it’s currently being used to circumvent controls deployed to filter content on your internet.
The Browser and OS Encryption War
DNS by design has been unencrypted since its original design, very similar to how web traffic was also unencrypted by design (i.e., HTTP vs HTTPS). The importance, and need, to encrypt the communication was amplified around abuses at the hand of Internet Service Providers (ISP) and Governments. It was all based on an entities ability to collect and analyze your online behaviors.
A few years back, Google and Lets Encrypt led the charge with tackling encryption on the web via the HTTPS protocol. But there was still a big void on the internet with the Domain Name System (DNS), which similar to HTTP was designed to be in clear text (a.k.a. not encrypted).
This brought about a big push for encryption at the DNS level, but unlike the web that uses one protocol (i.e., HTTPS), there were multiple interested parties and two encryption DNS protocols were introduced:
- DNS-over-TLS (DOT)
- DNS-over-HTTPS (DOH)
The big issue with these protocols comes down to who is sponsoring which, and how they are being released to the world.
By design, DNS has traditionally occurred at the system (e.g., Windows OS) / network (e.g., router) level but the new protocols allowed the introduction of a new player (e.g., browsers). This new change brings with it new challenges, specifically with DOH which operates over basic web traffic / ports (e.g., HTTPS / port 443). This means it’s almost indistinguishable for a user, or service, to differentiate and control the traffic.
The communities inability to work as a cohesive unit means that you, the consumers, will have to figure out how to differentiate the technologies and figure out your own ways to deploy controls to help mitigate their effects. Fun!
How Encrypted DNS Affects Parents and Schools
What does all this mean?
Put simply, the introduction of encrypted DNS is a great thing. The problem lies in how it’s being released, and it’s this release that is going to introduce holes in the way you manage your internet. Whether you’re using CleanBrowsing, or another service provider, there will be no way to get around Encrypted DNS and you will have to take action to help protect your internet.
All major browsers are now introducing Encrypted DNS in their browser settings as a “Secure DNS” option. This option allows the user to circumvent any network settings you might deploy (including content filtering).
When this Secure DNS option is enabled, this is what happens:
- If a parent, or organization, defines an acceptable use policy (i.e., filters content according to what they deem appropriate) DOH by design will bypass those controls;
- Kids are actively leveraging DOH features in their browsers to have unfettered access to the web, at home, and at school, and we’re seeing that happen with kids as young as single digits;
- Organizations are now left blind to the activity happening on their network, this applies to both benign and malicious activity;
This is further complicated because, by design, these same platforms don’t make it easy for parents or network administrators to manage this setting. The assumption is that all users on the device are the same, and the “child” use case is poorly accounted for. Larger enterprises have the tools, and knowledge, to better control these new features, but non-enterprise administrators are left to fend for themselves.
The good news is that there is a way to disable the Secure DNS option at the system level. Guide to Disable Secure DNS
The guide above is for Windows users. It will disable Secure DNS in Mozilla Firefox, Google Chrome, Brave, and Microsoft Edge browsers. If you couple this with non-Administrator profiles you will be on your way to better control what your users can do on their devices to bypass your content filtering controls.
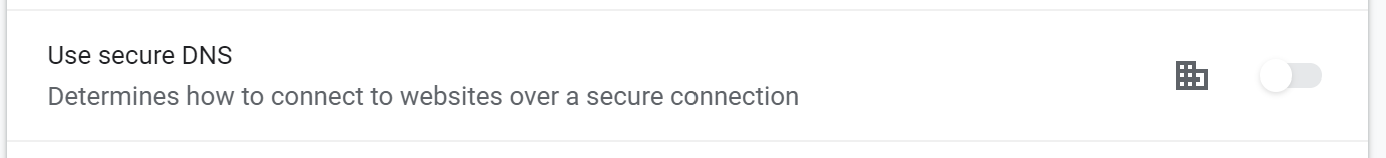
When deployed, the user will see the above image in their respective browser settings. Schools can leverage this registry file to deploy it to their fleet of devices, and parents can manually deploy it on their Windows machines.
We will work to prepare a similar option for MacOS users.
